- 404
- Home
- Remote Administration
- Employee Monitoring
- Information Security
- Features
- Live Employee Desktop
- Employee Internet Monitoring
- E-mail monitoring
- Keystroke Monitoring
- File Activity Monitoring Software
- Printed document tracking
- Optical Character Recognition (OCR)
- Smart rules & alerts
- Network activity monitoring
- App usage/application monitoring
- Instant Message Monitoring
- Remote Desktop Control
- Active vs. Idle Time Analysis
- Employee Productivity Tracking
- Linux terminal capture
- Nonproductive Activity Reporting
- Custom reports
- Session Recording & Metadata
- User Card
- Screen Capture
- Web-cam snapshots
- USB device control
- Data Leak Prevention (DLP)
- Voice communication recording
- File Scanner
- Software and Hardware Inventory
- Insider Threat Detection & Prevention
- Remote Employee Monitoring
- Privileged User Monitoring
- Productivity optimization
- Third Party Vendor Management
- Compliance Management, Auditing & Monitoring
- Cases
- GDPR Compliance
- For HIPAA
- For Legal
- Government & Public Sector Cyber Security
- PCI DSS Compliance & Certification
- General Data Protection Regulation (GDPR)
- Energy & Utilities Sector Cyber Security
- For Financial Sector
- Retail & Ecommerce Cyber Security
- About Us
- Why Us?
- Partners
- White Papers
- Support
- Pricing
- Request demo
- Solutions
- Purchase
- Demo request
- 404
- index
- Remote Administration
- Employee Monitoring
- Information Security
- Features
- Insider Threat Detection & Prevention
- Remote Employee Monitoring
- Privileged User Monitoring
- Productivity optimization
- Third Party Vendor Management
- Compliance Management, Auditing & Monitoring
- Cases
- GDPR Compliance
- For HIPAA
- For Legal
- Government & Public Sector Cyber Security
- PCI DSS Compliance & Certification
- General Data Protection Regulation (GDPR)
- Energy & Utilities Sector Cyber Security
- For Financial Sector
- Retail & Ecommerce Cyber Security
- About Us
- Why Us?
- Partners
- White Papers
- Support
- Pricing
- Request demo
- Solutions
- Purchase
- Demo request
Information Security
Activity Monitoring, User Behavior Analytics, Productivity Optimization & Insider Threat Detection in a Single Platform
Request demo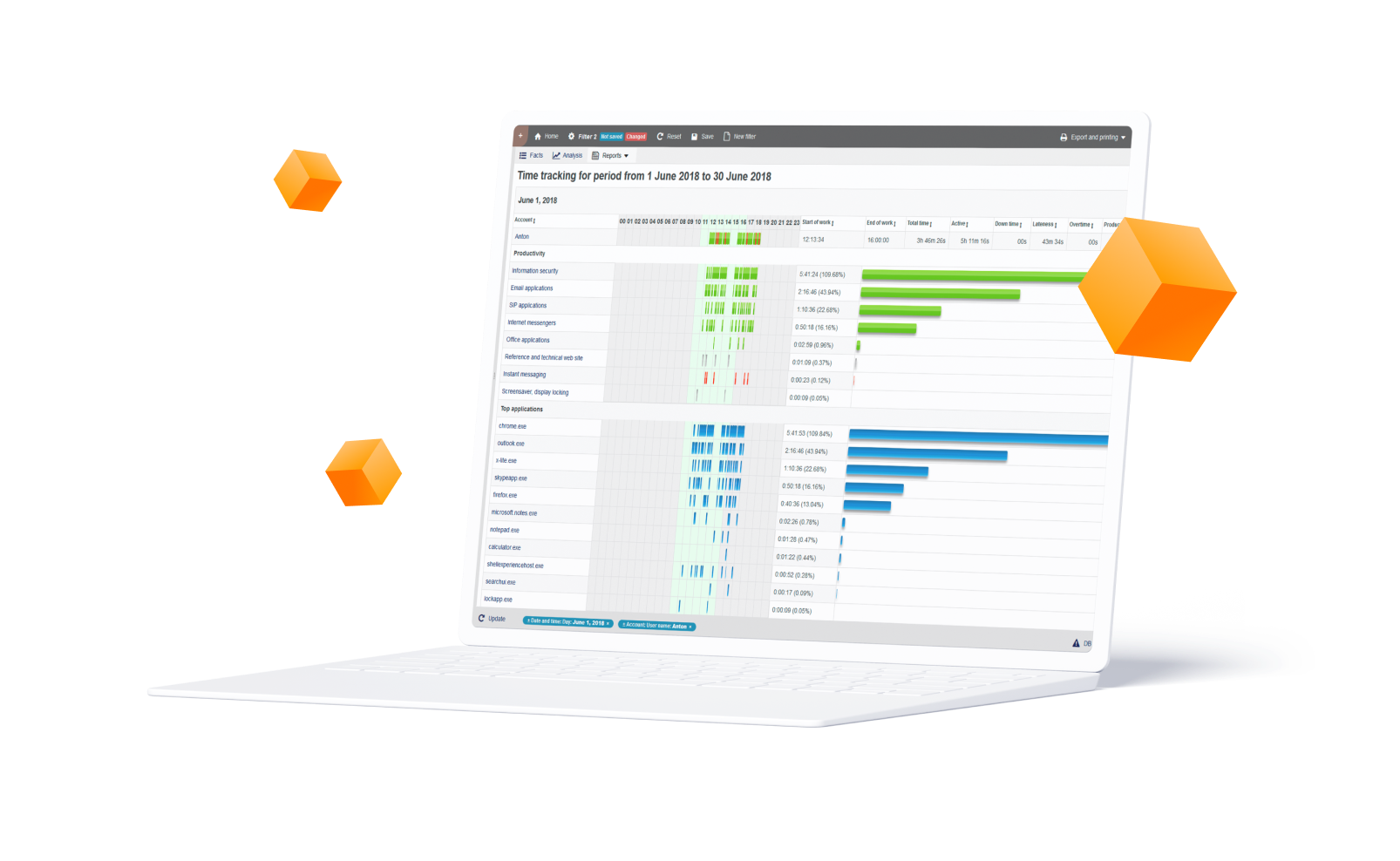
Effective defense against data breaches, data leaks and IP theft
Data Loss Prevention (DLP) is a strategy for ensuring your employees and vendors do not accidentally or intentionally share sensitive and company confidential data outside your organization. First, Identify what types of data and communication channels are sensitive. Next, create policies and rules for data usage scenarios. The system then monitors user actions; validates them against the DLP rules and takes appropriate action if and when a rule condition is triggered. Actions could include stopping the action, blocking the user, alerting an administrator, requesting management override and more.
DLP: Data loss prevention, user activity monitoring and insider threats detection in a single platform
‘User-centric’, endpoint Data Loss Prevention solution goes beyond traditional DLP approaches by adding intelligent behavioral analysis to identify human factors like malicious intent, errors or accidents allowing you to implement effective protection against data breaches and other exfiltration attempts. DLP provides the best return of investment for organizations of any size. It’s designed to assist SMBs, enterprises and the public sector address data loss, cybersecurity and insider threats. Additionally, StaffCop’s compliance management features help you conform with compliance regulations including GDPR, HIPAA, PCI DSS, and ISO 27001.
1
User activity monitoring
Monitors all user activity including third-party vendors and privileged users for 22+ system objects like: website, application, keystroke, IM, email, network etc
2
Powerful policy and rules engine
Comes with hundreds of pre-built rules, templates and data categories. Create your own rules with an intuitive, visual Policy & Rules editor
3
Insider threat detection
Detailed logs capture all web/app activity, duration, IP/URL. Filter the report for individuals, groups or department by productive- unproductive or custom categories. Real-time alerts and trend reports show what rules were broken, when, by whom, what action was taken and the context
4
Content discovery and classification
Discover and identify sensitive information from structured and unstructured sources with the help of customized vocabularies.
5
Advanced OCR
‘On the fly’ content discovery with advanced OCR, natural language processing (NLP) and RegEx. Detect sensitive data inside images and applications
6
Clipboard monitoring
Clipboard Monitoring and Interception feature allows you to protect sensitive data from being shared through the clipboard copy/paste operations
7
Fingerprinting and tagging
Powerful fingerprinting and tagging features identify important documents and files and then monitors their usage so that you can keep track of your data even when modified or transferred
8
Compliance Management
StaffCop Enterprise can significantly help you meet ISO 27001 demands. The flexibility of settings makes it perfect to fit any Information Security Management System (ISMS).
9
Risk management
Identify high risk users, policies and system objects on the dedicated Risk Dashboard. Sophisticated risk scoring helps identify and focus on high risk areas
Industry Statistics Prove the
Need for Employee Monitoring
Need for Employee Monitoring
Financial loss due to a data breach is huge
According to a 2018 study conducted by the Ponemon Institute, the average cost of a data breach rose by 6.4% with a range of $3.86M - $350M.
$3.86M avg. cost of a breach
$350% for larger breaches
User privilege puts sensitive data at risk
According to a survey of 400,000 member online by Cybersecurity Insiders published on The Insider Threat 2018 report.
37% Excess Privilege
34% Increased Amount of Sensitive Data
Data leak incidents are growing at an alarming rate
The rate of data breaches in 2018 reported by federal survey respondents is 57%, more than 3x higher than what they measured 2 years ago.
300% increase in data breaches in two years
Ip losses due to cyber crime is hurting companies globally
According to the Community Emergency Response Team, the main reasons for insider caused incidents are collusion from employees and third-parties.
~$60B is the upper range for annual global loss in IP
Information Security with StaffCop delivers Immediate
Business Benefits
Business Benefits

Block prohibited applications
StaffCop can not only track application activity but also prevent specified applications from launching. For example, corporate policy forbids usage of torrent clients on workstations. We can add uTorrent to the black list of applications. In this case, if a user tries clicking the shortcut or the .exe file itself nothing will happen. On the other hand, we can specify a list of applications that can be accessed, while ALL that are not in the white list will not work. For example, we add Word, Excel and Thunderbird to the list - the user will be able to launch ONLY them.
Block access to websites
You can use StaffCop to block particular web-sites that can be distracting or harmful for working process.
Black list. Add domains or URLs of web-sites that will be blocked. All other web-sites can still be accessed.
White list. Add domains or URLs of web-sites that will be allowed. In this example, we allowed access to StaffCop.com, Bitrix24 and Capterra. ALL other web-sites will be bloked. White lists are useful in case corporate policy allows working ONLY with a narrow range of web-sites.
Black list. Add domains or URLs of web-sites that will be blocked. All other web-sites can still be accessed.
White list. Add domains or URLs of web-sites that will be allowed. In this example, we allowed access to StaffCop.com, Bitrix24 and Capterra. ALL other web-sites will be bloked. White lists are useful in case corporate policy allows working ONLY with a narrow range of web-sites.


Powerful policy & rules editor
Flexible platform and powerful rules engine allows for creation of rules and policies to easily address data loss prevention needs of any organization. The visual Policy and Rules Editor enables administrators to define highly complex rules for very specific use cases with oversight on all internal and external disk activity, keystrokes, application usage, instant message and much more. Use black/white listing, define safe or restricted app and websites and do much more.
Block USB devices by IDs or classes
StaffCop provides flexible options for blocking USB devices on the basis of black and white lists. If you need to block particular devices, add their IDs to the "Block" list. All the other devices can be accessed. If you need to use only particular USB devices, add their IDs to the "Allow" list. ALL other devices will be blocked. The same principle can be applied for devices classes, for example, we can forbid usage of all external video/audio devices or to allow usage only of printers, keyboards and mouses.


Monitor Privileged Employees and Third-Party Vendors
Allows organizations to stop potential employee-employee or employee-third party collusion attempts. Create profiles for remote, privileged, external vendors and then define what information and system resources each profile can access. Further rules can be set up by behavior policies so that access to sensitive information is segregated by the organization’s security policy.
Reduce Organizational Risk and Protect Yourself with Proof
Take action against a malicious employee backed by solid proof. You can view detailed reports for all employees including any security incidents and what steps were taken. Instant snapshots, session recordings and history playback features can be used to view employees desktop for audit and evidence gathering purposes. Video and audio recording can be exported and shared with law enforcement authority.


Data breach audit with forensic evidence
Detailed alerts for all users can be viewed including any breach events and what actions were taken. Session recordings and history playback can be used to view user’s desktop for audit and evidence gathering purposes. StaffCop is a wayback machine! At any moment, you can go back in time and see what a particular employee was doing in a specified period in the past.
Data risk identification and management
First, determine what behaviors are high risk i.e. copying files to external drives, using cloud storage to share corporate files, downloading/opening files and attachments from unknown sources etc. Then, apply advanced behavior-based rules to automatically detect when employees violate the rules. Utilize sophisticated anomaly rules to identify employee activity outside the normal behavior. Immediately get notified about harmful employee activity, lock them out from the system or take remote control of their computer before any malicious or fraudulent attempt.

The Right Employee Monitoring
and DLP Solution for Every Need
and DLP Solution for Every Need

Information Security
Receive the required data “on the fly”. Search by keywords and regular expressions. Record sound from microphones to hear what was happening at the moment of interest.
.
Try for free 
Remote Administration
View remote desktop without being notices. Take control over a workstation. Full picture of software and hardware usage. Intensity of usage and registry of states.
Try for free Recommend

Employee Monitoring
Categorize applications and web-sites into productive and unproductive. Set up different configurations for particular users, groups and departments. Compare results.
.
Try for free Flexible Deployment Options

Bare Metal
Install on bare metal from our ISO image containing Ubuntu 18.04 and StaffCop or install StaffCop packages on existing Ubuntu 18.04.

Virtual Machine
Install on any OS as a virtual machine from our ISO image, use Virtual Box, VMWare, Hyper-V or any other virtualization system. Easy administrating without risking the host machine.

Private Cloud
Use your own secure, scalable private cloud implementation including AWS, Google Cloud, Azure and more
92% of companies detect serious violations when testing StaffCop



LEARN
Documentation SUPPORT
%201.svg?v=2020-10-15T10:37:02.579Z)

